How to Add User Authentication to a Chatbot in SaaS
Emma Ke
on April 3, 2026CMO
7 min read
Key takeaways
- Chatbot authentication matters when the assistant needs to know who the user is.
- It is especially important for SaaS products, portals, and logged-in support experiences.
- Start by defining the access boundary, then pick an auth model that fits your deployment surface.
- Related guides: white label chatbot and chatbot SDK.
Why chatbot authentication matters
A public chatbot can answer general product questions without knowing who the visitor is. But once the assistant needs to retrieve account information, tailor guidance to a user role, or trigger protected actions, user authentication becomes essential. OWASP defines authentication as the process of verifying that an individual or system is who it claims to be, which is the exact line between a public FAQ chatbot and an account-aware assistant (OWASP Authentication Cheat Sheet).
This article is for product teams, SaaS operators, and support leaders building assistants for logged-in environments. If your chatbot sits inside an account area, customer portal, or internal product, authentication is not an optional extra. It defines what the assistant is allowed to see and do.
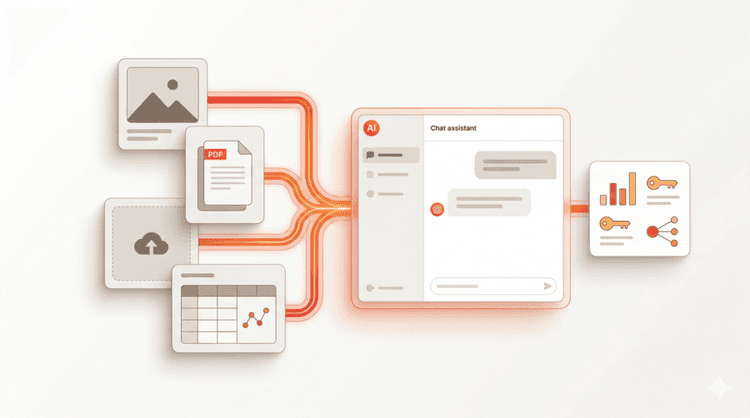
What chatbot user authentication means
At a practical level, chatbot authentication means the assistant can verify user identity before using sensitive context or performing protected actions.
That may include:
- matching the chatbot session to a logged-in app session
- passing signed user context into the conversation
- enforcing role or plan-based access
- restricting what actions the chatbot can trigger
Without these controls, the assistant is forced to stay generic or becomes a security risk.
Chat Data’s own product documentation is already specific here. The user authentication launch notes describe userId support up to 30 characters, userHash support up to 100 characters, and server-side hash generation using a secret key so the browser never exposes the signing secret (Chat Data user authentication changelog, logged-in user docs).
When you need a logged-in chatbot experience
1. Account-specific support
If the chatbot should answer questions like “why is my subscription paused?” or “what plan am I on?”, it needs user identity and permission-aware logic.
2. Personalized onboarding
Inside a product, the assistant can become much more useful when it understands where the user is in setup and what actions they have already taken.
3. Protected workflows
If the chatbot can update settings, retrieve private data, or submit requests to another system, authentication is a must.
4. Team or role-based experiences
An admin user and an end user should not necessarily see the same options, data, or workflow paths.
How to add user authentication to a chatbot
Step 1: Define the access boundary
Start by deciding exactly what the chatbot needs to know. The safest design is not “give the assistant everything.” It is “give the assistant only the context it needs for this workflow.”
Useful questions:
- Does the chatbot need the user’s identity or just their plan type?
- Should it access account history, billing, or support state?
- Which actions should require a stronger permission check?
Step 2: Pick the auth model
Common options include:
- existing logged-in web session
- SSO for enterprise environments
- signed user tokens or scoped session handoff
The right model depends on where the chatbot lives. Embedded product assistants often inherit app authentication. External-facing assistants may need a handoff step before they can access protected data.
For enterprise or reseller flows, SSO may be the better fit. Chat Data’s SSO launch notes position the feature for reseller environments that want branded access and admin control without asking end users to create a separate Chat Data account (SSO changelog, SSO setup docs).
Step 3: Separate general and authenticated flows
One of the simplest mistakes is trying to make every conversation authenticated by default. In most products, the better pattern is to let the chatbot handle public guidance first, then request or use identity only when the workflow actually needs it.
That creates a cleaner experience and reduces unnecessary exposure.
Step 4: Add role and action controls
Authentication tells you who the user is. Authorization determines what they can do. Your chatbot should not just know the user. It should also understand whether that user can access the requested data or trigger the requested action.
Step 5: Design safe fallbacks
If the chatbot cannot verify identity or lacks permission, it should explain the limitation clearly and route the user to the correct next step. Safe fallback behavior is part of good UX, not just security practice.
How Chat Data handles chatbot authentication
Chat Data provides several features that support authenticated chatbot experiences:
- white label chatbot -- branded access with SSO so end users manage chatbots under your domain
- chatbot SDK -- pass signed user context from your app into the chatbot session
- AI workflow automation -- build permission-aware workflows that depend on user identity
Authentication becomes more commercially meaningful when paired with white labeling, chatbot-specific API keys, and embedded SDK experiences. Chat Data's chatbot-specific API keys support up to 10 keys per chatbot, which matters when you want isolated access for clients, partner teams, or separate production surfaces (per-chatbot API keys changelog).
Common mistakes teams make
Treating authentication as a front-end detail only
If the assistant can call APIs or retrieve data, the backend permission model matters just as much as the visible UI state.
Giving the chatbot too much context
The assistant does not need unrestricted access to be useful. Over-scoping is both risky and unnecessary.
Ignoring fallback states
Users need clear guidance when the chatbot cannot proceed. That includes session expiration, missing permissions, and unsupported requests.
Mixing public and private content carelessly
Teams often forget to distinguish between what the chatbot can say publicly and what it can say only after the user is authenticated. That separation should be explicit.
Related resources
These guides cover related topics for building secure, account-aware chatbot experiences:
- White label chatbot -- deploy branded AI chat with SSO and isolated client access
- Chatbot SDK -- embed chat into your product with user context and event listeners
- AI workflow automation -- trigger APIs, route leads, and enforce business rules in conversations
- What is an MCP chatbot? -- connect your assistant to external tools and live data
FAQ
What is chatbot authentication?
Chatbot authentication is the process of verifying a user’s identity before the assistant accesses user-specific information or performs protected actions.
When do I need user authentication in a chatbot?
You need it when the chatbot works inside a logged-in experience, retrieves protected account data, or triggers workflows that depend on the user’s identity and permissions.
Is SSO the same thing as chatbot authentication?
Not exactly. SSO is one way to authenticate users, especially in enterprise environments. Chatbot authentication is the broader design problem of identity, access, and permission-aware conversation behavior.
Sources and implementation references
- OWASP Authentication Cheat Sheet
- Chat Data logged-in user authentication docs
- Chat Data user authentication changelog
- Chat Data SSO changelog
- Chatbot-specific API keys changelog
Conclusion
Chatbot authentication is not an optional add-on for product-embedded assistants. If your chatbot works inside a logged-in environment, accesses user-specific data, or triggers protected actions, authentication should be designed early rather than patched in after launch.
Start with the access boundary, pick the right auth model for your deployment, and build safe fallbacks for every permission-dependent workflow.